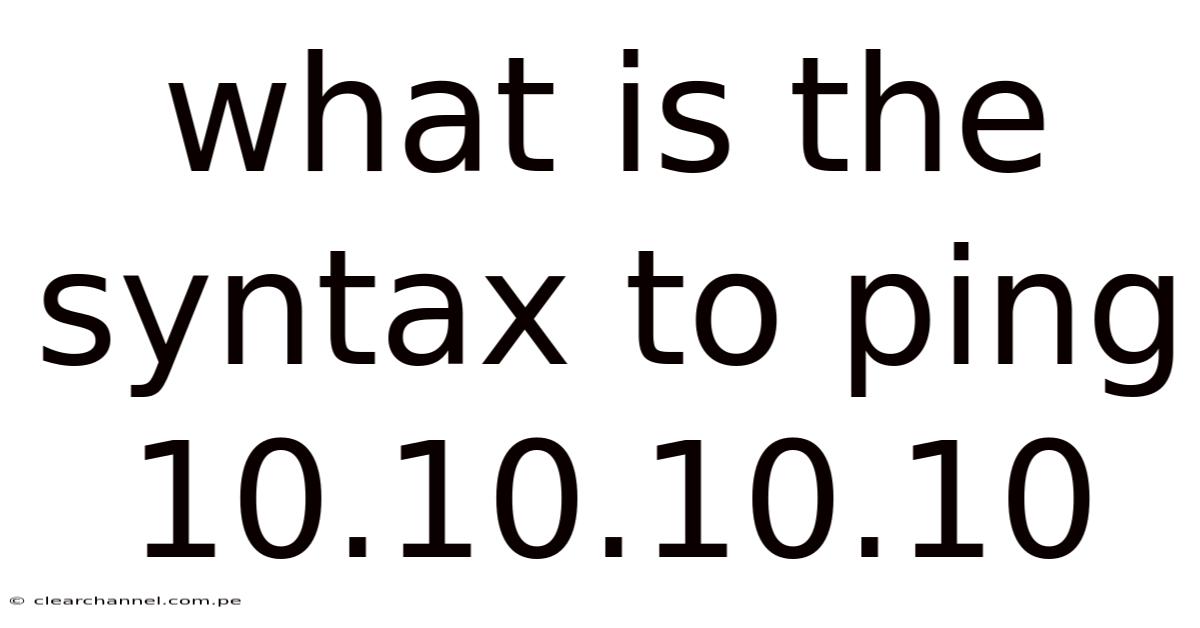
What Is The Syntax To Ping 10.10.10.10
The act of pinging a specific network address serves as a foundational tool within the realm of network diagnostics, offering immediate insight into the state of connectivity that connects a device to a particular host. This practice, often referred to as a ping operation, acts as a diagnostic probe, revealing whether a target machine is reachable, its responsiveness, or potential bottlenecks within its network path. In an era where digital communication relies heavily on seamless connectivity, understanding and executing ping commands becomes indispensable for troubleshooting issues, verifying system configurations, or simply confirming that devices are properly synchronized across a network. Whether managing a small office environment or overseeing a large-scale infrastructure, the ability to assess network performance through such straightforward commands underscores its critical role in maintaining operational efficiency. Such tasks demand precision, as even minor misconfigurations or delays can cascade into broader system failures, necessitating meticulous attention to detail. The process itself, while seemingly simple, involves layers of technical knowledge and practical application that collectively contribute to the overall reliability of network operations. It is within this context that mastering the syntax for pinging 10.10.10.10 emerges as a pivotal skill, enabling users to navigate the complexities of modern network environments with confidence. This foundational knowledge serves as a cornerstone upon which more advanced troubleshooting techniques build, ensuring that network administrators and technicians remain equipped to handle a wide array of scenarios effectively.
Pinging, at its core, is a command-line utility designed to test the reachability of a specified IP address by transmitting ICMP packets to determine if the destination host is accessible and functioning. The fundamental syntax for executing this command hinges on the basic structure of network diagnostics, where the target address is succinctly inputted into the command line. In this case, the target becomes 10.10.10.10, a placeholder often used as a test dummy address in documentation or for illustrative purposes. However, understanding the precise mechanics behind such a command involves recognizing the components involved: the "ping" itself, the target address, and the protocol used (ICMP), which operates at the network layer of the OSI model. Each element plays a distinct role in conveying whether the communication path remains open or if obstacles exist. For instance, the "ping" function sends an echo request back to the receiving system, expecting an immediate response, thereby acting as a direct measure of response time and connectivity status. The target address, in this instance, must be accurately specified to ensure the system can resolve it correctly, avoiding ambiguities that might lead to misinterpretation. The syntax remains consistent across platforms, though slight variations in command execution may arise depending on the operating system or toolset employed. Regardless of the environment, the core directive remains unchanged: a precise command that directs traffic toward a specific destination. This consistency allows for standardized procedures when collaborating with teams or documenting processes, ensuring uniformity and clarity. Furthermore, the act of pinging itself requires familiarity with the underlying principles of network protocols and the nuances of how different systems interpret and respond to ICMP responses. Misunderstanding these fundamentals can lead to frustration or missteps, underscoring the importance of thorough preparation before executing such commands. In practice, the process unfolds in a sequence of steps where the user inputs the command, waits for the system’s response, and interprets the outcome to inform subsequent actions. Whether analyzing latency, detecting packet loss, or verifying service availability, the immediate feedback provided by the ping command serves as a critical input for decision-making. This immediacy makes pinging a tool not just a diagnostic measure but a dynamic tool that adapts to real-time conditions, allowing users to pivot swiftly based on the results. The ability to execute pings effectively thus becomes a skill that enhances problem-solving agility, enabling practitioners to address issues proactively rather than reactively.
Subheadings such as "Understanding the
Understandingthe limitations and nuances of ICMP-based diagnostics is equally vital as mastering the command syntax itself. While ping provides invaluable baseline connectivity data, its simplicity also introduces constraints that practitioners must recognize to avoid erroneous conclusions. For instance, many networks employ firewalls or security policies that explicitly block ICMP echo requests/replies at the perimeter or between segments, rendering a "no response" result ambiguous—it could indicate genuine host unavailability, deliberate filtering, or transient network congestion. Similarly, high latency or packet loss observed via ping might stem from QoS policies deprioritizing ICMP traffic rather than actual path degradation, especially in congested enterprise or service provider environments. Interpreting results therefore requires contextual awareness: Is the target known to permit ICMP? Are other services (like HTTP or SSH) functioning normally despite failed pings? Cross-referencing with application-layer tests or tools like traceroute (which maps the path hop-by-hop using TTL-exceeded messages) or mtr (which combines ping and traceroute with continuous monitoring) often provides a more complete picture.
Advanced ping usage further refines diagnostic precision. Adjusting packet size (-s on Linux/macOS, -l on Windows) helps identify MTU-related issues causing fragmentation or silent drops. Varying the interval between requests (-i) can uncover intermittent problems obscured by default timing. Setting a specific timeout (-W or -w) prevents indefinite hangs during troubleshooting scripts. Capturing verbose output (-v) or logging results to a file enables trend analysis over time, transforming ping from a spot-check into a monitoring component. Crucially, recognizing that a successful ping only confirms L3 reachability—not application-layer service health—prevents overreliance; a host may respond to ICMP while its web server is crashed or its database port is firewalled. This distinction underscores why ping remains a starting point, not an endpoint, in systematic troubleshooting.
Ultimately, the enduring value of the ping command lies not in its complexity, but in its accessibility as a universal network "heartbeat" check. Mastery involves moving beyond rote execution to cultivating a diagnostic mindset: knowing when to deploy it, how to interrogate its output critically, and what complementary evidence to seek when results are ambiguous or misleading. By grounding this skill in a solid grasp of IP fundamentals, ICMP behavior, and real-world network quirks, technicians transform a simple utility into a powerful instrument for maintaining network integrity—proactively isolating faults, validating changes, and ensuring the foundational pathways upon which all higher-level services depend remain open and responsive. In an era of increasingly complex, dynamic infrastructures, this foundational proficiency remains indispensable for effective, agile network stewardship.
Looking ahead, the role of ping—andthe underlying principles it embodies—will only grow more pertinent as networks evolve toward automation, intent‑based operations, and zero‑touch provisioning. In software‑defined environments, where policies are instantiated dynamically across virtual fabric layers, a simple ICMP echo can serve as a lightweight health probe that feeds directly into orchestration engines. For instance, a controller might trigger a burst of pings to a newly instantiated service mesh node; if the response rate falls below a predefined threshold, the controller can automatically roll back the deployment or reroute traffic to a standby instance. This tight feedback loop underscores how ping can be integrated into larger, programmable workflows without sacrificing its simplicity.
In cloud‑native architectures, where containers spin up and down in seconds, traditional network diagnostics must adapt. Here, tools such as ping are often wrapped in side‑car containers or executed via Kubernetes Jobs to validate service endpoints during rolling updates. Because containers share the host network namespace, a ping from within a pod to an external IP reveals whether the pod’s egress path is intact and whether the underlying overlay network (e.g., VXLAN, Geneve) is functioning as expected. Moreover, the granularity of container‑level resource constraints means that variations in ping latency can hint at CPU throttling or memory pressure, providing early warning signs before more severe performance degradation occurs.
Security considerations also shape how ping is employed in modern environments. While many administrators once relied on ICMP as a benign diagnostic, malicious actors have leveraged ping sweeps to map reachable hosts during reconnaissance. Consequently, network segmentation strategies now often enforce “ICMP permit” policies selectively, allowing only trusted management interfaces to emit or receive echo requests. Understanding these policy nuances prevents accidental exposure of internal topology while still preserving the ability to perform essential connectivity checks. In zero‑trust models, where every hop is treated as potentially hostile, a ping may be replaced or supplemented by encrypted health probes—such as gRPC health checks or TLS‑wrapped TCP connections—that convey similar reachability information while adhering to stricter security postures.
Another layer of evolution is evident in the rise of observability platforms that aggregate metrics from diverse sources. Here, ping data can be time‑stamped, tagged with service identifiers, and fed into dashboards that visualize latency trends across microservices, geographic regions, or even specific physical links. When combined with machine‑learning anomaly detection, subtle shifts in ping round‑trip times can trigger alerts long before human operators notice a degradation, enabling proactive remediation. This data‑driven approach transforms a historical, ad‑hoc troubleshooting method into a cornerstone of continuous performance assurance.
In practice, mastering ping therefore involves more than memorizing command‑line switches; it requires cultivating a mindset that treats every echo request as a query about the network’s current state, a hypothesis to be tested, and a piece of a larger puzzle that includes routing tables, firewall rules, application health, and infrastructure scaling decisions. By internalizing the underlying protocols, recognizing environmental constraints, and integrating ping into broader automation and observability frameworks, practitioners can wield this elementary tool with the sophistication demanded by today’s complex networks.
In summary, the humble ping command remains a vital sentinel in the network engineer’s toolkit. Its simplicity belies its capacity to reveal deep insights when used thoughtfully, contextually, and in concert with complementary techniques. As networks continue to expand in scale, dynamism, and complexity, the ability to interpret ICMP responses—while respecting security boundaries and leveraging modern observability—will remain a foundational competency for anyone charged with designing, operating, or troubleshooting modern communications infrastructure. This enduring relevance ensures that ping will continue to serve not merely as a diagnostic command, but as a guiding principle for maintaining reliable, responsive, and secure network ecosystems.
Latest Posts
Latest Posts
-
A Shift In The Supply Curve Reflects A Change In
Mar 28, 2026
-
Which Of The Following Best Captures Our Objective In War
Mar 28, 2026
-
What Are Two Phases Of Bloodstain Pattern Interpretation
Mar 28, 2026
-
Air Brakes Cdl Test Answers Pdf
Mar 28, 2026
-
The Term Photoautotroph Refers To An Organism That
Mar 28, 2026